How Generative AI Is Transforming Marketplace SEO in 2026
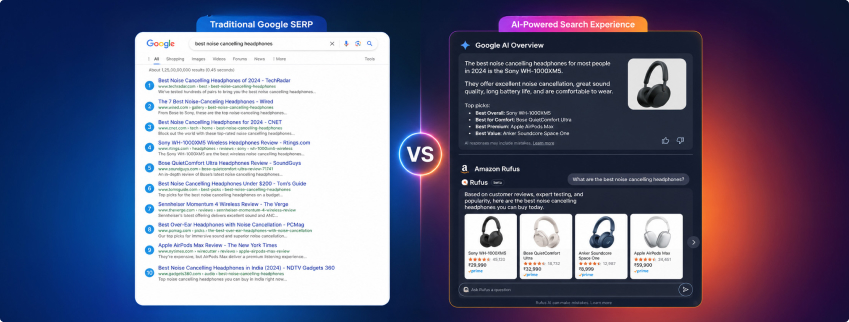
Marketplace SEO is no longer just about ranking on page one. Generative AI — from Google AI Overviews to Amazon Rufus and ChatGPT — is intercepting buyer intent before users even reach your listings. To maintain visibility, sellers must optimise listings for AI readability, build topical authority, implement structured schema, and monitor AI citation share alongside traditional rankings. Generative AI SEO combines GEO, AEO, and LLM optimisation to ensure brands are cited where purchase decisions are increasingly made.